Insights, Page 1
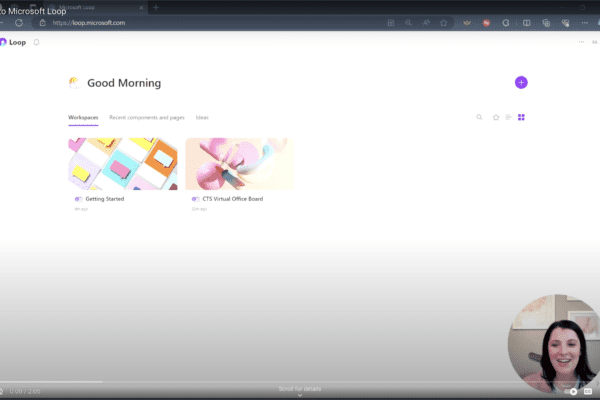
How to create a workspace with Microsoft Loop
March 9, 2024
Wondering how to get started with Microsoft Loop? Here’s how to create a workspace. One of our favorite aspects of Microsoft Loop is its ability to streamline ideas and project management within… Read more
Introduction to Microsoft Loop
February 22, 2024
What exactly is Microsoft Loop? It’s not just another tool—it’s a transformative platform reshaping the way teams work together in real-time. Gone are the days of scattered communication and disjointed workflows. Seamlessly… Read more
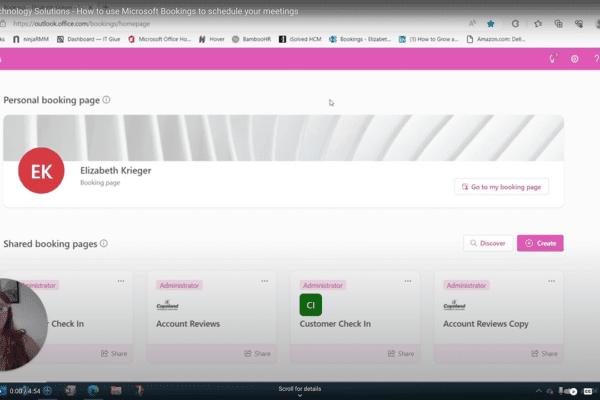
How to use Microsoft Bookings to schedule your meetings
August 15, 2023
Have you ever found yourself lost in a sea of chats, struggling to locate that crucial piece of information from a few weeks or days back? With the Control-F function, you can… Read more
Copeland brand refresh five year anniversary
May 11, 2023
It’s hard to believe it’s already been five years since we unveiled our brand refresh. Looking back, it was a pivotal moment for Copeland. It marked a shift in how we presented… Read more
What is vulnerability scanning?
March 29, 2023
Just because you’re not using an application doesn’t mean it’s not vulnerable. Vulnerability scanning is a platform that will look for weaknesses on the systems and hardware that live on your network…. Read more
Is your classic Antivirus Software Protection enough for today’s threats?
March 8, 2023
Endpoint Detection and Response is a next-generation tool similar to Antivirus (AVP) but uses AI features to detect threats on your system and recover from them. This software may also include a… Read more
How can you automate tasks that you do on your computer frequently to save you time?
January 31, 2023
There are two options to choose from: You can use Power Automate Desktop. This is a free program that you can install on Windows 10. With Windows 11, Power Automate Desktop is… Read more
Why you should off-board former users immediately
November 30, 2022
Why should you off-board users as soon as they are no longer with your organization? This is a very important process that helps keep your company assets secure from unauthorized access. It… Read more
How to increase the quality of your video in a Teams meeting
October 20, 2022
How can you increase the quality of your video while in a Teams meeting? You can now adjust your brightness and soft focus on your camera which enhances your video quality when… Read more